- Select Language
The U9000 handheld PDA combines advanced barcode s...
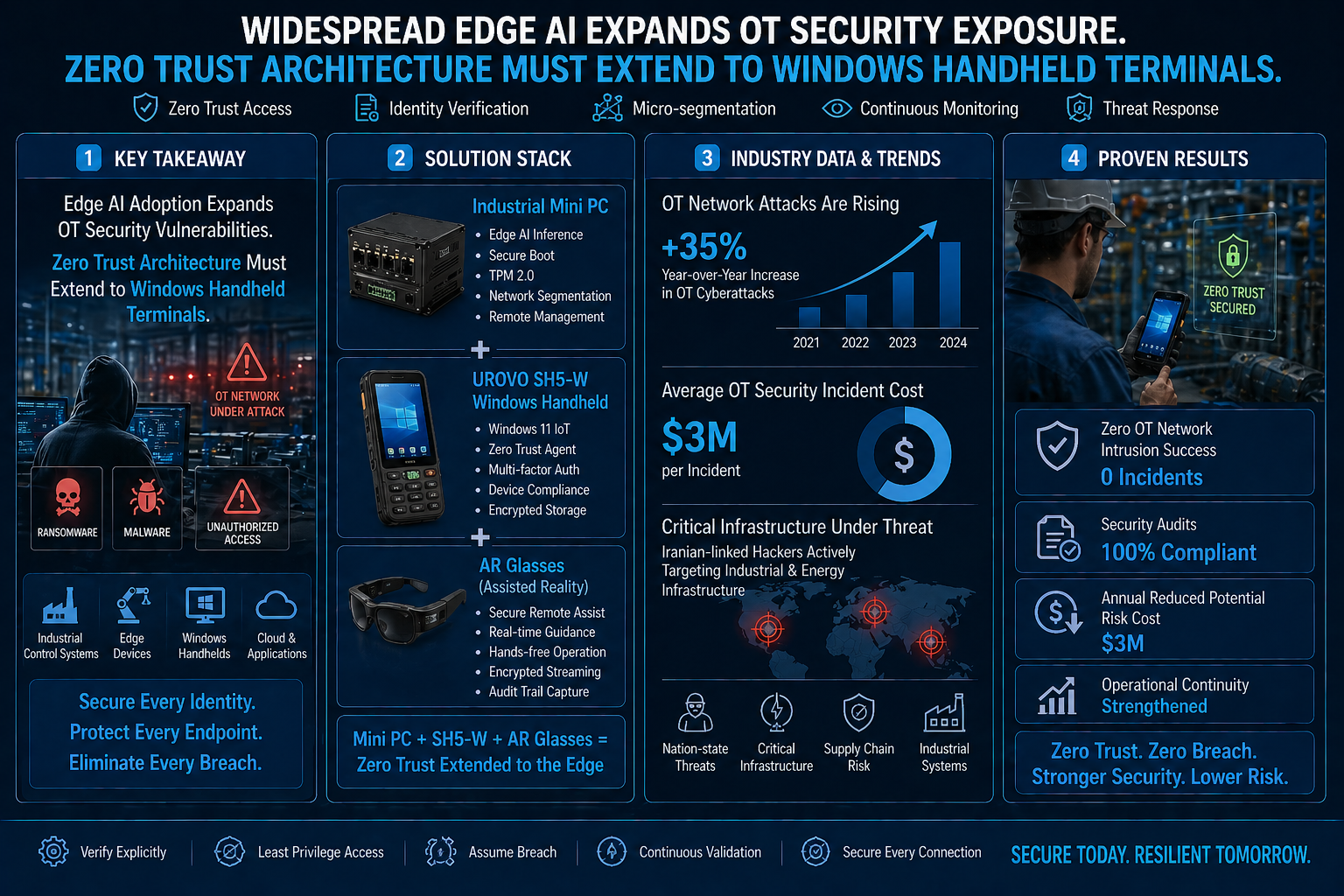
Fig 1 – Edge gateway enabling secure segmentation in industrial OT networks
Industrial connectivity is expanding rapidly, but security practices are not keeping pace. As more legacy equipment is connected to edge systems, the risk of unauthorized access increases unless strict control mechanisms are applied at every layer.
Industrial Cybersecurity | Edge Computing Security | April 2026
Edge computing is becoming a core component of modern industrial systems. By processing data closer to machines, organizations achieve faster response times and improved operational efficiency. However, this shift also introduces new entry points into operational technology (OT) networks.
Many industrial devices—such as PLCs, sensors, and legacy controllers—were not originally designed for secure network connectivity. When these systems are connected to edge gateways without proper safeguards, they become vulnerable to intrusion.
Common risks include:
Addressing these risks requires a shift from perimeter-based security to a zero trust model.
Zero trust architecture assumes that no device or user should be trusted by default. Every access request must be authenticated, verified, and continuously monitored.
The Hotus industrial Mini PC serves as a secure edge gateway within this framework. It enables controlled communication between field devices and enterprise systems while enforcing strict security policies.
Core security capabilities include:
By isolating critical systems and restricting data flows, the edge gateway minimizes the potential impact of a breach.

Fig 2 – Secure handheld device used for controlled access to OT systems
Human interaction remains a necessary part of industrial operations. Technicians frequently access systems for maintenance, diagnostics, and updates. Without proper controls, these access points can introduce vulnerabilities.
The Hotus SH5-W rugged Windows handheld is designed to support secure field access. It integrates enterprise-grade security features that align with zero trust principles.
Security features include:
This ensures that even if a device is lost or compromised, unauthorized access to critical systems is prevented.
Fig 3 – Hands-free monitoring interface with controlled data visibility
In environments where operators need constant mobility, minimizing direct interaction with devices can further enhance security.
The AR smart glasses provide a controlled interface for viewing system data without exposing credentials or requiring physical input. Access can be limited to authorized users through identity verification methods such as voice recognition or proximity validation.
This approach reduces the likelihood of credential leakage while maintaining operational efficiency.
Implementing zero trust principles across edge devices and mobile endpoints delivers measurable benefits:
These advantages are particularly important in critical infrastructure and high-availability environments.
A robust OT security strategy integrates multiple layers of protection. A complete framework includes:
By aligning edge computing deployment with zero trust architecture, organizations can scale industrial connectivity without exposing critical systems to unnecessary risk.
As edge AI adoption accelerates, integrating security into every device and connection point is essential for maintaining reliable and resilient industrial operations.